Electronic Voting Security Challenges
“Cyber Revolution”… a catchy expression we use these days! This type of “revolution” is conducted over the Internet using social networks, such as Facebook and Twitter, and this is the first time in history that people start a revolution against unfair and oppressive government systems by a Cyber Revolution.
To help maintain the principles of this revolution and sustain it to use it anytime we are again confronted by governments that lack freedom of speech, we should put some “controls” into our lives to guarantee as much as we do not reinvent the wheel, especially while no political party is in control and there is some sort of chaos around a certain country. That is the time to put neutral controls over Cyber Revolution.
I said “controls”, right?! Yes, I did. Does not this remind us, Security Professionals, of something we used to use in our daily life when referring to Firewalls, IPS, IDS, etc. But what type of controls am I talking about?!
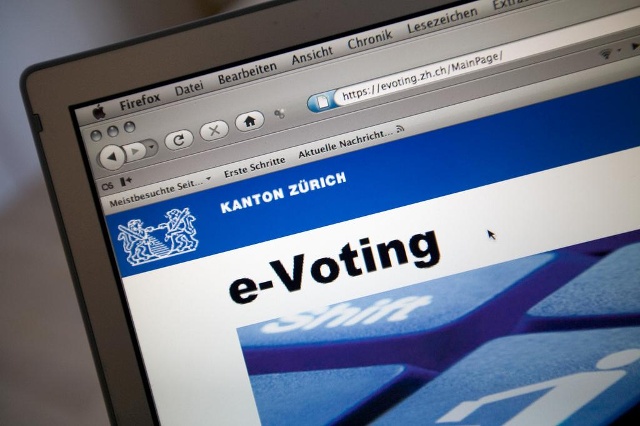
As we all know, the main objectives of Information Security is to protect the confidentiality, integrity and availability of our company, our organization and our country. What I see right now is that people believe in this revolution and to help them trust it more and more is to have a system that makes them feel secure and safe when they give their votes during elections or referendums. We are talking here about “Electronic Voting”.
I know that the idea is not new, and that it has been implemented in lots of countries such as the USA, Spain, Australia, and the Netherlands – just to name a few – either by Remote E-Voting or Polling Place E-Voting. However, these systems are not easy as you might think; they are complex systems that depend on a voting software by a virus or a bug then you might have an undesirable president or parliament member for example. Therefore, due to its critical risks and that some countries already had voting fraud incidents, Electronic Voting needs to be assessed and analyzed well to check whether it is can be applied safely in our country. Basically a voting system has four main characteristics;1
1. Accuracy: The goal of any voting system is to establish the intent of each individual voter, and translate those intents into a final tally. To the extent that a voting system fails to do this, it is undesirable. This characteristic also includes security: it should be impossible to change someone else’s vote, ballot stuff, destroy votes, or otherwise affect the accuracy of the final tally.
2. Anonymity: Secret ballots are fundamental to democracy, and voting systems must be designed to facilitate voter anonymity. This also means confidentiality, in one way or another.
3. Scalability: Voting systems need to be able to handle very large elections. With the increase of population, we need to invest on something that could sustain along enough.
4. Speed: Voting systems should produce results quickly. This is particularly important where people expect to learn the results of their voting on the same day it took place, before bedtime or early the day after, and monitor the progress of the voting process.
So, these are the four main features that should characterize Electronic Voting, and if we have a system that can do that electronically then this will guarantee neutral and falsification freevotes. Electronic Voting can be used in presidential elections, parliament members’ elections and also inside the parliament while voting for legislations and policies. We need to forget about the previous “funny” way by which votes inside the parliament were handled and move to E-Voting; the Speaker of the People’s Assembly of Egypt used to
just check the votes for legislations and policies only by the eye!
Let us see how we can implement the Electronic Voting system; usually the system will machines all over the country to collect the votes. These machines are connected in a secure way to a central point for analysis and monitoring. So if we spread our devices over 700 sites for example, and then the central point notices that some suspicious activities then investigations may start and track any distrustful activity. But what kind of machines should be used?! Maybe a PC, but it can be infected by a virus or a worm. Maybe a hardened machine! How can these machines be connected to the sites.
countries like Brazil, India, USA, are Direct-Recording Electronic (DRE)2 voting machines. A DRE machine records votes by means of a ballot display provided with mechanical or electro-optical components which can be activated by the voter (typically through buttons or a touchscreen). Then data is processed by means of a computer program.
Then voting data and ballot images are recorded in memory components. After the elections, the DRE machine produces a tabulation of the voting data as a soft copy stored on a removable memory component and as a hard cop as well.
The system may also provide a means for transmitting individual ballots or vote totals to a central location for consolidating and reporting the results by precincts at the central point. So data can be transferred securely through encrypted links or flash memories with backup so as to maintain confidentiality and integrity of data. And by having the backup, availability is guaranteed.
These DRE machines should be hardened and certified through audits, so as to ensure security. For sure machinesmay differ from one type of election to another, but the concept is the same.
Figure 1 DRE Machine used in Brazil
I believe that in order to have “Cyber Revolution”, we need to implement systems in our countries which bring technology into our daily lives. And since secure voting is a crucial step in bringing trustworthy entities for the sake of serving our people, then special attention should be paid to deploying “Electronic Voting” in our countries.
References :
1- Adopted from Bruce Scheier Blog – Schneier on Security
2 -Definition as per Wikipedia
About the Author:

Mohamed Enab, Five Years of Experience in Information Security Consultation Field & possess deep knowledge and understanding for security threats & countermeasure, security products & technologies, Information security management systems, networks & operating systems. Having been in Banking Field for 2 years where Money talks and Security is a great concern there and also in Information Security Consultation Field giving consultation and advisory actions to customers to get the best of the breed from security solutions and secure the organizations which have different concerns & Business Objectives. I have right now Security Certifications like CISSP, CCSP, SSCP and have a good networking/Telecommunication background.