A Simplified Approach to Achieve Security in a Consumerized Environment
Abstract:
This paper looks at simple ways that can be adopted by anyone into their IT environment. Without a doubt, those ways greatly help Information Security personnel to strike the right chord between security and consumerism.
Introduction:
Consumerization is the latest catch phrase in the workplace. With the growing penetration of broadband and mobile technologies, the tools used in the workplace are changing rapidly. Earlier equipments and technologies used to be released in enterprises and then in marketplaces, but this trend is highly reversing nowadays.
They are introduced first in the marketplace, and then, they make their own way into enterprises. Facebook, iPhone and Google Android are typical examples. A recent Unisys study, conducted by IDC[1], exposes a troubling gap between the activities and expectations of new generations of iworkers, and their employer’s readiness to manage secure rand support this movement and capitalise on it. Capitalising the movement means boosting productivity by facilitating it with new ways of connecting and sharing,
staying competitive as an innovative company and a workplace, and of course delivering IT flexibly while managing security.
These are various methods on how the security personnel can go about to achieve the right balance between IT security and consumerization.
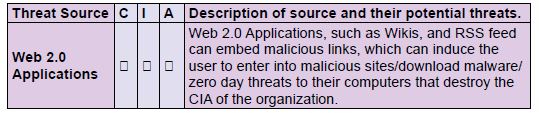
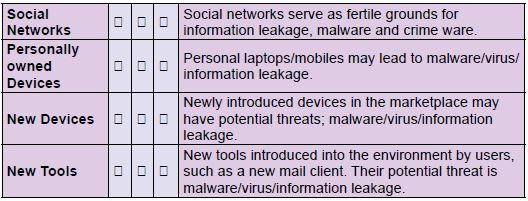
Know your Threats:
Knowing and documenting the source of threats is the first basic step. A simple documentation template is shown below. The purpose of this template is to serve as an example and it is intended for it not to be complete.
Classify Data:
Information security professionals should be highly aware of which kind of data needs to be secured. They must assess which information is valuable and which is not, and be able to strike the balance between protecting custodial data, secret data and usual business data. According to a 2010 Forrester research study, security teams need to focus more on protecting secret data that provides longterm competitive advantages such as mergers and acquisitions product plans, earning forecasts and trade secrets, and other data that damage their reputation rather than protecting usual business data.
Example earning reports of many public listed companies are posted into their websites which need not be protected at all.
Establish Sound Security Policies:
At the minimum, an information security policy revolving around consumerisation must contain the following.
1. Mandatory encryption of any company owned secret/custodial data on their personally owned mobiles/devices
2. Mobile devices that are used for business must have the potential to have their data remotely wiped
3. Mandatory health checks of laptops connecting to the corporate network via network access protection to be performed to ensure that the laptops adhere to the security standards of the company
4. Mandatory encryption of communications in transit between employees owned devices and the company network via VPN
5. Enforce sync parsing to control which data types can be synchronized between mobiles and the computer of the organisation
6. Enable the biometric technology on company owned mobiles
White List Consumer Software:
Consumer software are those that can be used on the computers of the organisation, such as Skype, iTunes, etc, and then they are easily published on the organisational portal. In addition, this list is circulated through other internal communication mechanisms of the organization. Any other consumer software that needs to be used will be incorporated into this white list only after getting the go ahead from the “IT Security Team”.
Information Security Awareness Campaigns:
Reigning in a comprehensive information security awareness campaign will measure the awareness level through frequent and infrequent quizzes and tests. Thinking of various methodologies on how best to reach out to all employees within the organization, and involving all employees of the organization right from senior management to contract employees are two things to be taken into consideration.
Enforce Policy Monitoring Tools:
Once policies are understood and accepted, then comes the need to enforce policies and monitoring tools just to ensure compliance to the same. This is where technology comes to our rescue. The usage of technological tools, such as VigilEnt Policy Center, will ensure the levels to which policies are being followed in addition to reporting deviations on a real time basis.
Restrict Mobiles in Designated Areas:
The usage of mobile equipment in sensitive areas such as the data center should be restricted, and monitoring the data center 24/7 through a CCTV camera is essential. Certain steps like maintaining the records of the CCTV camera for at least a period of 3 months is recommended. This can be securely disposed off or archived with necessary approvals.
Employ Location Based Technology:
This is a new trend in technology which uses Global Positioning Systems Information security managers and personnel can monitor in real-time the location of employees and limit or
disable their ability to access sensitive information, and they can go on conducting sensitive transactions in areas, such as coffee pubs, etc. The use of advanced technologies such as these
will also enable security professionals to track employee’s activity when he/she is deploying overseas.
Deploy Virtualized Desktops:
When virtualised desktops are deployed, employees can access information on their personal devices; but the core infrastructure and data remain on corporate servers behind the firewall.
Separate Networks Based on Data Access:
Creating separate VLANs for data accessed from home and other locations will ensure that the core corporate network is available in the event of an incident occurring due to malware/spyware, etc. Moreover, creating separate VLANs for accessing corporate data using personally owned devices ensures that rogue equipment do not get directly connected to the corporate network without the help of an insider.
Deploy NAC/NAP:
Implementing Network Access Control/ Network Access Protection ensures that personally owned devices and mobiles that connect to the corporate network have met the security standards of the company in reference to antivirus/latest patches and so on.
Incident Management System: In spite of best efforts, a security incident canvery well happen in a consumerised IT environment; so having a mature incident management system in place is vital to isolate the incident and to ensure the availability of systems, which will both lead to the continuity of the business.
Change Management Methodology:
Employing robust change management methodologies is important to ensure that all new tools/devices which are to be used in accessing data from the corporate network will need to go through a change management process. This helps to make sure that all consumer items are evaluated properly before they are released into the corporate environment.
CMDB:
Benchmarking all consumer software, tools, devices and equipment as per good security practices, and having a configuration management database for all tools/devices will ensure that any new devices, that fall under this category, will match to these new standards. Creating awareness to everyone using internal communication mechanisms is a must.
Deploy Integrated End Point Solutions:
Deploying integrated end point management solutions with a centralised management console is required to ease the administration effort required from security administrators.
References:
[1]: http://www.unisys.com/unisys/ri/topic/researchtopicdetail.jsp?id=700004.
Conclusion:
While consumerisation is a healthy phenomenon, the security threat brought about is real. Security administrators can take simple proactive steps such as these to address threats brought about by consumerisation. By using the right mix of processes, procedures, awareness and tools, they can always ensure security and consumerisation which are in sync with each other.
About the Author:
Vinoth Sivasubramanian : I am currently working with UAE Exchange Center LLC as Manager – IT Audit. I have around 7+ years of experience in information security
in various domains such as finance, telecommunication and consulting. My great passion towards information security is the secret of my success. I am also a member of International Cyber Ethics, and an ISSA educational advisory committee member. You can contact me on the following email-address:
[email protected]