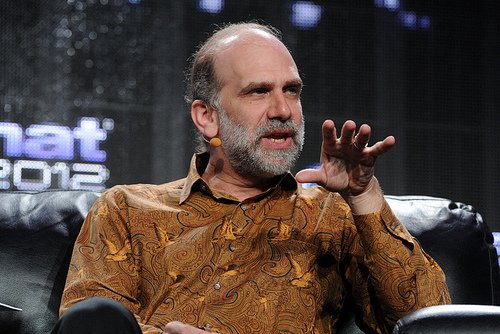
Book Review: Beyond Fear by Bruce Schneier
Each and everyone of us makes security decisions every day, sometimes even without thinking about it. Should i buy items with my credit card or is doing so too risky? Should i park in the underground parking slot or is it safe enough to park on a side-street next to the building? How often should i brush my teeth? These are some of the many security decisions we make every day.
But how often do we stop to think: are we making ‘good’ security decisions or ‘poor’ ones?
Are our decisions based on fear, uncertainty, and doubt, or are our decisions based on real information and a repeatable decision-making process?
In his book “beyond fear: thinking sensibly about security in an uncertain world” bruce schneier takes a critical look at not only what constitutes good security, but also highlights the many trade-offs that we often make in the name of security. He then proposes a process to enable us to consistently make solid security decisions. Bruce suggests the following 5-step process:
Step 1: what assets are we trying to protect?
Clearly defining the assets that we are trying to protect is crucial and is often overlooked. Failing to do so can result in deploying a security solution that is ineffective, costly and risky. For example, securing an airplane, an airport, and passengers are all different security problems that require different security solutions. In fact, a security solution to one of these assets can actually increase the risk to another.
Step 2: what are the risks to the assets?
This step involves performing a risk assessment including: what are the threats we are protecting against, what is the impact of a successful attack, and what are the attack vectors that may be exploited. Depending on the criticality of the security decision, we can perform either a quick informal risk assessment or perform a full-fledged risk assessment based on any of the known risk frameworks (nist sp800-30, fair, octave, etc.).
Step 3: how well does the security solution mitigate those risks?
Once we have identified the main risks that we wish to address, it’s time to review security solutions. This step goes beyond simply looking at security solutions and how well they work. It involves verifying that the security solution actually does what the vendor claims.
It also involves understanding how the solution interacts with everything around it, including how the solution fails.
Step 4: what other risks does the security solution cause?
Many people overlook the fact that the introduction of any new system (even a security system) adds new security problems. We have to ensure that these new problems are smaller than the ones that we originally addressed.
Step 5: what trade-offs does the security solution require?
Every security decision involves trade-offs: money, time, operational overhead, inconvenience, diminished freedoms, poor employee or customer satisfaction, and more. All too often, security decisions do not take these trade-offs into consideration, leading to poor decisions that may often be reverted downthe road, either due to unforeseen costs or resistance from employees and customers. Moreover, alienating employees and customers can be disastrous as security revolves around people.
Having completed the process, we are now finally in a position to decide: is this a good security decision or not? Is the benefit of mitigating the risks worth the added risks introduced by the solution and the trade-offs involved?
This process can be used not only for us to make better security decisions, but to also evaluate security decisions taken on our behalf whether it be by institutions or governments. For example, governments sometimes impose extra security checks in certain areas, monitor citizens, and take extra measures in response to possible threats. You can apply bruce’s process to conclude whether these decisions are solid or simply a means by governments to gain greater power and limit our freedoms.
The book is also packed with useful nuggets of security information that challenge your standard way of thinking of security such as simple but effective
methods to protect your home from robberies that you never thought of and how adding security controls to your car can get you killed in russia. You’ll look at how security decisions are often influenced by multiple players, each their own power and agenda.
You’ll look at how technology balances the scale in favor of attackers, how to negotiate for security, and how systems fail. Not only does the book go into much greater detail, but bruce also has a knack for making complex ideas sound simple, something we in the security field sorely lack and can greatly benefit from when talking to non-security colleagues and management.
I highly recommend you read “beyond fear” (and subscribe to bruce’s blog -Https://www.Schneier.Com/). Too often security decisions are knee-jerk reactions to a security breach. These decisions often do more damage than good while giving us a false sense of security. It’s time for us to start making good security decisions based on solid information and a well-defined and repeatable process.
About The Author
Osama Elnaggar, Information Security and Risk Manager at Etisalat