Using Cain and Able as an Intrusion Detection System
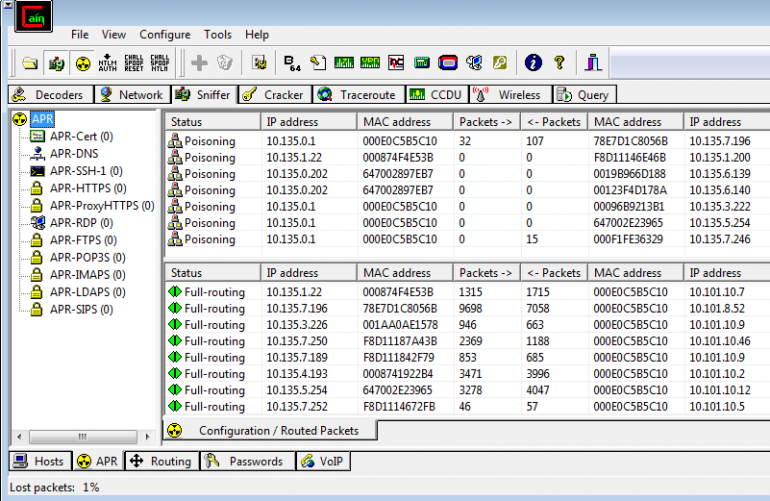
It was a normal day, doing some security consultant work for a company, I got no Alerts from their corporate Cisco IPS, also nothing from the open source IDS installed inside the network, I was testing for any anomaly on the network so I ran Cain and Able on a mirrored (span) port on the main, as expected I did not find any clear text passwords for corporate services (I’ve followed the usual approval process before running Cain and Able in the network) but then I noticed something strange, I saw the user name of one of company users, beside his user name was the password “123”, I was sure that no service in the company would transport passwords in clear text, so I decided to look deeper, I found also another user name with the same password but from different IP address, then the same users again with password “1234”, all of this was using the pop3 mail protocol, they do not allow the use of pop3, but the service was
not closed yet from the server, what was more alerting was the use of e-mail accounts that were already disabled long ago because the users have already left the company, then my doubts hit the roof.
I went to the next step, behavioral analysis, which I did it manually, I collected all of the pop3 logins, usernames, passwords and IP sources, what I found was fun, I had four IP sources, all of the pop3 usernames came from these four IPs, timing between each of them is more than 10 seconds, but changing, also the IPs are used interchangeably, I can summarize my finding to be as follows:
An attacker who is skilled and extremely very patient was using a script to change the IPs, he had the list of the email contacts (a lot of them were not in use anymore), he would try a password from an IP, then use the same password to test another account using another IP, this way when he finishes his testing for that password, he will not be detected, also the lockout counter would reset itself because he never tries the wrong password on the same account within the lockout period.
I admired his skills, but what I couldn’t understand is his patience, he was using a dictionary attack that would never work in an organization that knows the basics of Information Security, his methods would take months or even years before finding a correct password, I kept watching his attack and I was ready to disconnect him whenever he gets closer. I caught this attack by pure luck, I don’t think any IDS would have raised any alerts for such attacks, I know Malwares use similar attacks but they are usually programmed to exploit a vulnerability not testing e-mail passwords, that’s why I suspect this is a normal ongoing attack.
About The Author

Haitham Mohamed Saad, Information Security Specialist at Ministry of Interior of Qatar