Killing Android Mobile SIM Cards Using USSD
Are you using a mobile phone that runs Android as an Operating system … please note you are in danger and the danger will not affect just your mobile, including all its data but also the SIM card.
Can you imagine that a single line of code embedded in a web page can be used to trigger a remote factory reset of some Samsung smart phones, including the Galaxy SI, SII, SIII and also the HTC One X running HTC Sensation (Ice Cream Sandwich), the Motorola Droid series and the Google Nexus series.
What is USSD and what is it used for.
– I’m sure that you have used USSD Code before? It’s the code that’s enclosed between the * and # characters
– USSD stands for (Unstructured Supplementary Service Data) and is a session based GSM protocol unlike SMS or MMS.
– Typically it’s used to send messages between a mobile phone and an application server in the network. Nowadays there are multiple Services based on USSD, such as:
1. Mobile banking (Airtel Money in India, Vodafone money transfer in Kenia)
2. Social networking (Facebook, twitter)
3. Updating mobile software over-the-air
4. Pre-paid phone top-up and balance queries
In this article, I will discuss how to play with USSD codes using different tools and how to exploit different services based on it.
In addition, critical security issues in USSD based services such as virtual money transfer/mobile banking and social networking will be discussed, and last, I will discuss what exactly the term ‘dirty use of’ means.
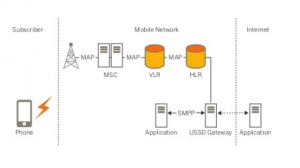
USSD Architecture
1. Architectural components:
2. MSC (Mobile Switching Center),VLR (Visitor Location Register)
3. USSD Gateway
4. USSD application/server
5. Simple Messaging Peer-Peer interface
What is the back door in Android OS:
» The vulnerability is in the dialer itself ( ex: TouchWiz in Samsung devices ) it fails to differentiate between dialing a phone number and USSD codes
» The web browser handles the “tel:” protocol, but as you know from above , the dialer can’t differentiate between calling numbers or USSD code
» So simply, the device can be forced automatically to open a link to such a page by touching a NFC-enabled phone to a rogue NFC tag, opening wap push messages, scanning a QR code or by including the link in a special service message. However an attacker can also include the link in a Twitter feed, MS or an email message and trick the victim to manually click on it.
5. How this vulnerability can be used as an attack:
1. Apparently it can also be triggered from a browser like this: <frame src=”tel:<insert the ussd code here>%23” />
Examples of USSD code which can be used on Samsung devices
a. Reset to Factory Settings : *#7780#
b. Full Factory Settings : *2767*3855# (Factory Hard Reset to ROM firmware default settings)
c. Factory Data Reset *#*# *#7780#*# (Clears Google-account data, system and program settings and installed programs. System will not be deleted, and OEM programs, as well as My Documents (pictures, music, videos))
2. QR Code to enforce the Mobile to run the USSD Code which injected in the link (you could also use www.goo.gl to change the URL)
3. Near field communication (NFC) victim can only see the show, can’t stop it (Galaxy SIII vulnerability can be exploited)
4. Wap push message also to open a link that is injected
To burn the SIM card
» In a normal situation you can change a Pin code (**05*1234545*1234*1234#) but if 3 wrong pins are entered, à Sim card gets locked and will ask for a PUK code
» 10 wrong PUK codes will kill the SIM card forcing you to buy a new one.
How to prevent the USSD attack:
1. Install Telstop from the Google play store. This tool will mitigate the USSD attack by publishing a URI handler for TEL. Every time a TEL URI is activated an application selector will be shown.
Or
2. Install Dialer One as an alternate dialer for your android devices. A tel: URL will now prompt for the application to use.
About The Author
Mohamed Zain, Senior Linux Systems Engineer